

The Pleasures and Pitfalls of Collecting and Presenting Electronic Evidence
by
Melissa F. Brown & Kenneth G. Raggio
For “civilians”, the parts about Call Spoofing at the end is quite informatve
A. Anecdotal Fact Situation 1
You are at your client’s deposition. Questions are asked that you and your client agree that there is no way the other side should know to inquire about unless they had access to confidential communications with the lawyer.
What is going on?
B. Anecdotal Fact Situation 2
Your client, the wife, suspects that her husband has an interesting personal and financial life with their small business outside of her knowledge as a stay-at-home mom. She sees the second page of a tax return – enough to see the place for her to sign – every year for 12.5 seconds. She knows that her husband keeps his laptop computer with him everywhere, but she does not know whether he owns it personally or whether his employer owns it.
How do you get, use, and possibly present the potential goldmine of data on the notebook computer?
C. Anecdotal Fact Situation 3
Wife is sure that her husband is not only smoking dope/cheating on her/whatever, and tells him she has proof of same – in writing. Your client, the husband, says she must have gotten into his Facebook/My Space pages.
How do you advise your client?
D. Anecdotal Fact Situation 4
Husband suspects wife is having an affair. He decides to follow her. He wisely tells his business lawyer, who refers him to you for a consultation. He is in your office, describing the above.
What’s next?
E. Anecdotal Fact Situation 5
The wife discovered her husband was involved in an affair. The husband admitted to the affair and admitted he communicated by email with his paramour. The wife informed her daughter-in-law of the situation. The daughter-in-law knew the husband had a Yahoo email account and correctly guessed the password and security questions to access the account. She then printed copies of emails from the account and gave them to the wife’s divorce attorney. The husband sued the wife, the daughter-in-law and the attorney alleging several violations, including violations of the Stored Communication Act (SCA). ( Jennings v. Jennings, SC Sup Ct.)
What possible issues? What result?
F. Anecdotal Fact Situation 6
Father and Mother are in a post divorce child custody dispute. A call to 911 indicates that an armed robbery is in progress at Mother’s apartment that is also the child’s home. The Swat team arrives and knocks, and then busts down the door. A surprised Mom tells the cops nothing is happening, that she made no call, and that the Father must have done this. The Police, just doing their job to make sure she and the child are not in danger, search the place, and find graphic evidence of Mom’s new career as an oil wrestler. The police incident report reveals that the 911 call originated from Mom’s phone, but there is no phone found on the premises when the police were there.
Despite assertions and some evidence that Father spoofed the 911 call, can he use the evidence from the report in his custody case?
G. These situations and variations thereof are the basis of this article and of the live presentation. Much has been written about procuring electronic evidence and use of it in a family law case. Few pleasures exceed exposing a lying spouse with their own words—or actions. But there are many pitfalls between the “birth” of such data and the use and presentation of it.
Melissa Brown’s attached article Safety and Security in a Digital Age is a primer on many ways that electronic evidence is legally and illegally collected. The time of presentation will not allow exploration of all species of illegal evidence collection and use, but rather will focus on a few areas.
This article will evolve. Later versions can be retrieved from www.raggiolaw.com/electronic-evidence or from www.scdivorcelaw.com/electronic-evidence. The materials will not repeat the excellent materials presented by Carole Gailor and by Jim Hennenhoffer and Gordon Cruse and at last year’s Midwinter meeting, but will leverage those presentations.
The presentation will discuss various views of a particular problem, from the generation of data all the way through a judge’s impression of it in court.
A. Types of Evidence that is Out There
1. Traditional Discovery
2. Traditional Surveillance
3. “Enhanced” Surveillance
B. If Electricity (or a Battery) Powers It…
C. Life is Not So Simple Anymore..
A. Client “Stupid”
1. Passwords/Access to Data
2. Emails and Texts
3. Social Media Postings and Settings
4. Cell Phones
5. Recordings, when legal/not legal
6. Stalking
7. Does Arrogance Sometimes Equal Ignorance?
B. Lawyer “Stupid”
1. Spoliation by Ignorance – Duty to Preserve, ( Lester v. Allied Concrete )
2. Duty to Inform Client to Preserve See National Law Journal article.
3. Knowledge of Illegal Evidence
a. Reliance on Client’s Representations ( US v Wuliger)
b. Client Cannot Disclose Illegal Evidence ( Peavy v WFAA-TV, Inc.)
4. Minnesota State Bar v Thomas Lowe (2013 )
“Compound” stupidC. Make client aware of technology that could be used against them even if it is illegal
1. Spoof/Trap Call card See attached photos.
2. Locational Recording devices (GPS device or GPS software in a smart phone, etc)
3. Keystroke Logger & Other Trojans
4. Don’t Forget Traditional Surveillance
A. Computer Hard drive – Showing to get and Chain of Custody to present
B. “Hard” Evidence
C. Electronic Evidence -8 step procedure to obtain ESI ( In Re Weekly Homes ) (Texas Supreme Court-discusses lot of Federal and other states’ cases. For 8 steps see pp21-22)
D. Websites/Facebook/Twitter
E. Individual Items on Websites, blogs, Facebook and Twitter such as posts, comments or photographs
A. Wiretap Act ( O’Brien v O’Brien —spyware on home computer)
B. Stored Communications Act 18 USC 2701
C. The Computer Fraud Act 18 USC 1030
D. Electronic Discovery Act
E. Electronic Communications Privacy Act
F. Federal Truth in Caller ID Act of 2009 47 USC 227 (e)
G. State Acts, using Texas, New York, and South Carolina as examples
A listing of [some] of the 50 states’ Computer anti-hacking laws:
http://www.irongeek.com/i.php?page=computerlaws/state-hacking-lawsH. After-the-Fact Civil Remedies Available to the “Wronged” from the “Perpetrator(s)”
VI. Use of Electronic Evidence
A. See V above FIRST
B. Discovery Requests and Acquisition of Evidence
C. Evolving Trends
1. Emails ( Zubulake I and Zubelale III fromWikipedia; White v White, NJ-2001 )
2. Reply Letter Document
3. Text Messages ( Christou v Beatport ) US DC, CO 2013
4. Internet Website Postings ( Tienda v. State )
5. Chat Room Content
6. Invasion of Privacy
D. Stored Data Versus Processed Data ( Garcia v City of Laredo )
E. Hearsay or Not
F. Authentication
G. Lorraine v Markel test
1. Relevant (FRE 401)
2. Authentic (FRE 901 (a)-902)
3. Not Hearsay (FRE 801-807)
Original or Duplicate (FRE 1001-1008)
Probative value vs. unfair prejudice (FRE 403)
A. The answer sheet to the Anecdotal questions.
B. Guide to Cases
Events that have come to light in the recent past
The following screen shots from a real live cell phone show how incredibly simple it is to spoof a call. The recipient’s caller ID will show a call incoming from, say the father’s phone. And her bill will prove that Mom received what she says was an harassing call at the time she received the spoofed call.
Celebrities have been abused this way-Katie Couric recently in New York and various movie stars in Hollywood. AND NO ONE HAS BEEN CAUGHT YET.




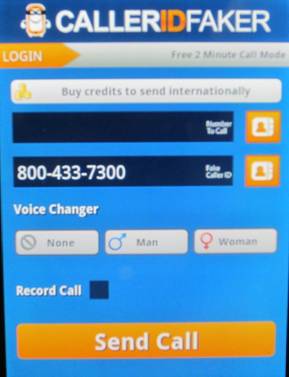

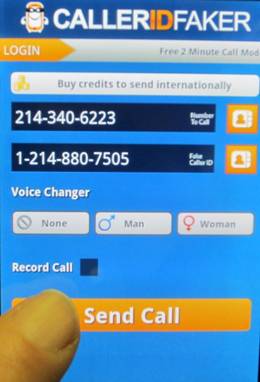
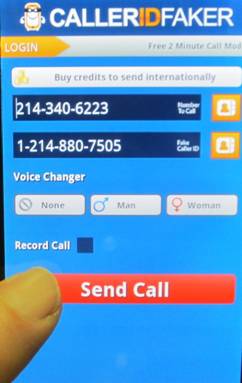
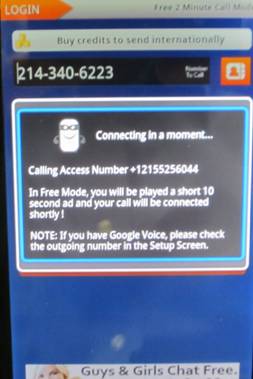

Adds a new dimension to “apparent authenticity of ESI, doesn’t it?
THE END!?!





